- Vitalik Buterin shared on X a new framework that redefines security as intent alignment.
- Growing exploits show failures come from user misunderstanding, not cryptography.
- Redundant checks, simulations, and AI-assisted tools will shape future Ethereum security.
Vitalik Buterin has published a groundbreaking security framework on X on February 22, 2026. He redefines security as actively closing the gap between users’ true intentions and the system’s actual behavior in crypto systems. Recent exploits prove most massive losses occur when users sign harmful transactions they misunderstand, not when cryptography fails.
Why “Perfect Security” In Crypto Is Impossible
According to Buterin, perfect security cannot exist. He explains this by showing that “user intent” is too complex to be fully defined or encoded. He illustrates this with the simple action of sending 1 Ethereum (ETH) to Bob, explaining that Bob is “a complicated meatspace entity that cannot be easily mathematically defined,” so representing him with a public key always risks sending funds to the wrong or compromised address.
As user goals grow more complex, the problem worsens. He cites privacy as an example, noting that encrypting messages alone is insufficient because metadata and timing patterns can still leak sensitive information.
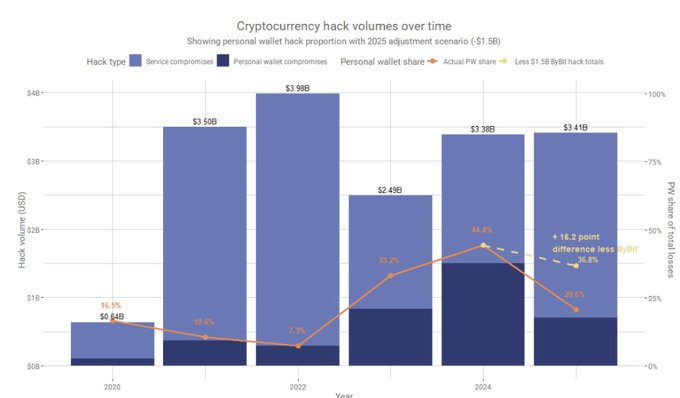
According to Chainalysis, the DPRK’s $1.5 billion hack of ByBit, the largest single hack in crypto history, accounts for the majority of service losses. By the end of June 2025, 17% more value had been stolen year-to-date (YTD) than in 2022, previously the worst year on record. Vitalik’s analysis shows why intent misalignment creates such catastrophic tail risks in practice, emphasizing that no amount of perfect code can overcome the inherent fuzziness of human goals.
What Are the Recommendations?
According to Buterin, a strong system’s security relies on its redundancy rather than perfection.
“Anything that the user can input into the system is fundamentally far too low-complexity to encode their intent fully,” Buterin stated.
Good systems, therefore, require users to specify their intention in multiple overlapping ways, and the system acts only when these signals align. Formal verification similarly requires developers to write mathematical properties alongside the code, and the system flags mismatches before deployment.
In crypto wallets, transaction simulations show users the expected on-chain consequences before they confirm, while multisig, social recovery, spending limits, and new-address confirmations add extra layers of approval for unusual or high-risk actions.
What This Means for Ethereum and AI Tools
Buterin has suggested that this security framework will shape the development of Ethereum wallets, smart contracts, and related hardware. Furthermore, Buterin stated that EIP-8141 advances customizable, intent-focused wallets with multisig and simulations. Low-risk actions stay easy; unusual ones get extra checks.
Notably, Buterin stated that LLMs simulate common sense to approximate intent from a new angle. As such, they never act alone but add one signal beside the rules and confirmations. This layered approach boosts safety without extra user friction.
Consequently, the future of security is not more clicks; it is smarter systems that detect unusual behavior and intervene only when necessary.
Related: Buterin Warns Against AGI Race, Pushes Decentralized AI Vision
Disclaimer: The information presented in this article is for informational and educational purposes only. The article does not constitute financial advice or advice of any kind. Coin Edition is not responsible for any losses incurred as a result of the utilization of content, products, or services mentioned. Readers are advised to exercise caution before taking any action related to the company.







